STM32F411 Secure Boot Lab Series
Author: Shafeeque Olassery Kunnikkal | Category: IoT, IoT Security, STM32F411 | Leave a Comment
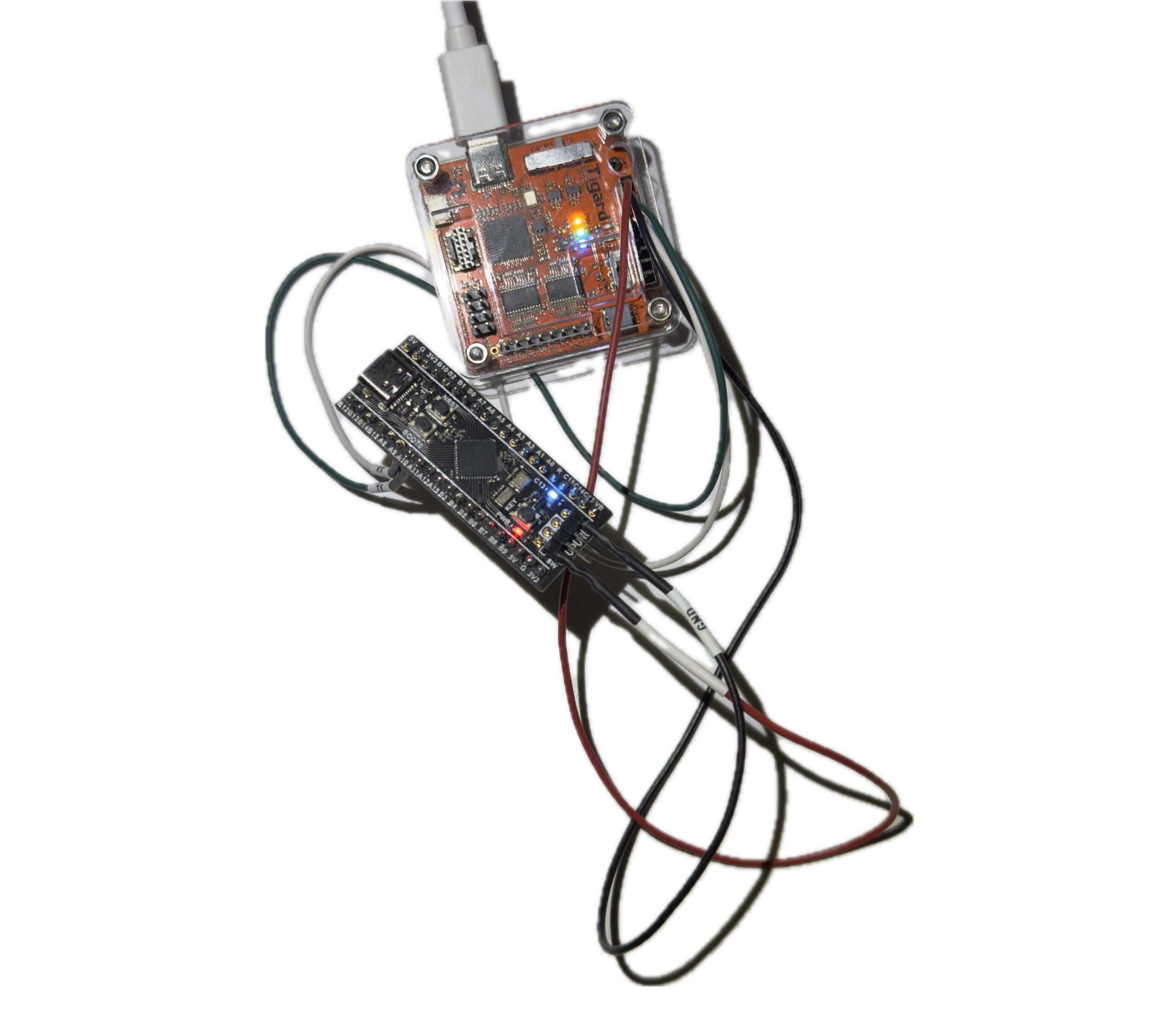
This series documents my work building and extending a compact cryptographic secure boot lab on the STM32F411CEU6 Black Pill.
The project started as a focused firmware integrity exercise: build a bootloader that validates a signed application image using SHA-256 and ECDSA-P256, verifies its vector table, and refuses to boot if anything is wrong. From there, the lab grew into something more useful: a reusable platform for fail-closed validation, hidden trigger analysis, binary diffing, and reverse engineering in Ghidra.
The goal of this series is not just to show a working demo. It is to document the decisions, debugging, validation work, and next-step research that turn a one-off embedded project into a defensible security lab.
Repository: This STM32F411 secure boot lab series is part of my broader IoT_Projects GitHub repository, where I collect IoT, embedded security, and firmware research projects.
Part 1: Building the Secure Boot Chain
The first part covers the implementation of the secure boot chain itself: flash layout, bootloader design, application placement, signing flow, Mbed TLS integration, linker corrections, VTOR relocation, and the debugging work that made verified boot succeed.
Read Part 1: Building a Compact Cryptographic Secure Boot Chain on STM32F411
Part 2: Validation, Hidden Triggers, and Reverse Engineering
The second part moves beyond the happy path. It focuses on fail-closed validation, an interrupt-driven hidden UART trigger inside the payload, and shaping the firmware into a better target for binary diffing and reverse engineering in Ghidra.
Why This Series Matters
Secure boot is one of those topics that sits at the center of embedded security. It touches firmware trust, memory layout, linker behavior, startup assumptions, debugging discipline, and later hardening steps such as write protection and readout protection.
That is why I like this STM32F411 lab as a research platform. It is small enough to be practical, but rich enough to support future work in tamper testing, firmware comparison, reverse engineering, and defensive analysis.
More parts may follow as the platform expands into hardening, binary diffing, and Ghidra-driven firmware analysis.
A secure boot lab becomes much more useful once it moves beyond the happy path.
